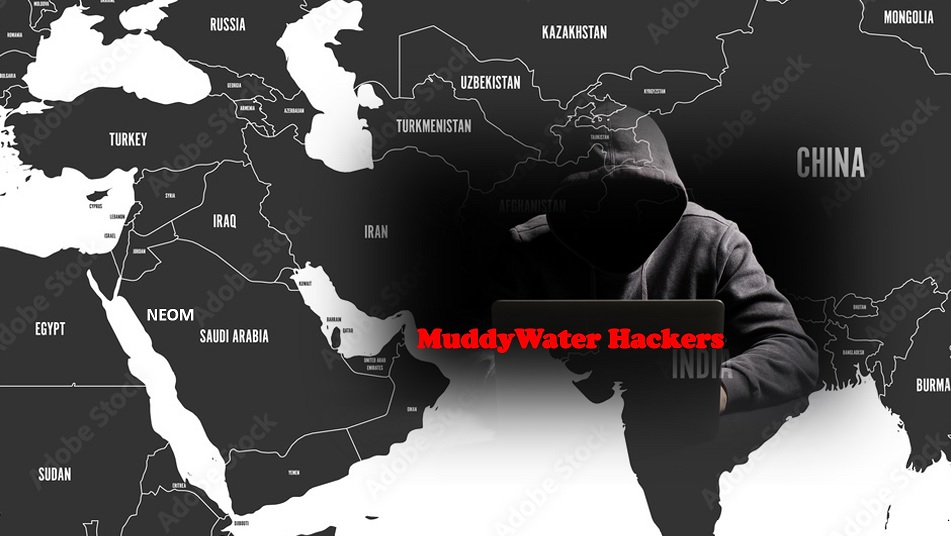
MuddyWater Hackers Target Asian and Middle East Countries
The Iran-linked MuddyWater threat actor has been observed targeting several countries in the Middle East as well as Central and West Asia as part of a new spear-phishing activity.
“The campaign has been observed targeting Armenia, Azerbaijan, Egypt, Iraq, Israel, Jordan, Oman, Qatar, Tajikistan, and the United Arab Emirates,” Deep Instinct researcher Simon Kenin said.
Dr Zakir Hussain Security & Policing Advisor said Muddy water is active since at-least 2017 and attacks mounted by the espionage group have typically targeted telecommunications, government, defense, and oil sectors. Now Muddy water Hackers targeting Smartcities, Conginitve Cities and other critical infrastrcture.
MuddyWater, also called Boggy Serpens, Cobalt Ulster, Earth Vetala, Mercury, Seedworm, Static Kitten, and TEMP.Zagros, is said to be a subordinate element within Iran’s Ministry of Intelligence and Security (MOIS).
The current intrusion set follows MuddyWater’s long-running modus operandi of using phishing lures that contain direct Dropbox links or document attachments with an embedded URL pointing to a ZIP archive file.
The threat actors are sending messages from already compromised corporate email accounts, which are being offered for sale on the darknet by webmail shops like Xleet, Odin, Xmina, and Lufix anywhere between $8 to $25 per account.
Early this year, Paul Nakasone, commander of the U.S. Cyber Command, speaks during a House Intelligence Committee hearing on April 15, 2021 in Washington, D.C. The U.S. and its allies will face “a diverse array of threats” in the coming year, with aggression by Russia, China and Iran. Pentagon said, The Iran is behind MuddyWater hacking group
Iranian intelligence is behind a group of cyber-attackers that have targeted private and government organizations across the Middle East.