State-Sponsored Hackers are conducting ransomware attacks against healthcare and critical infrastructure
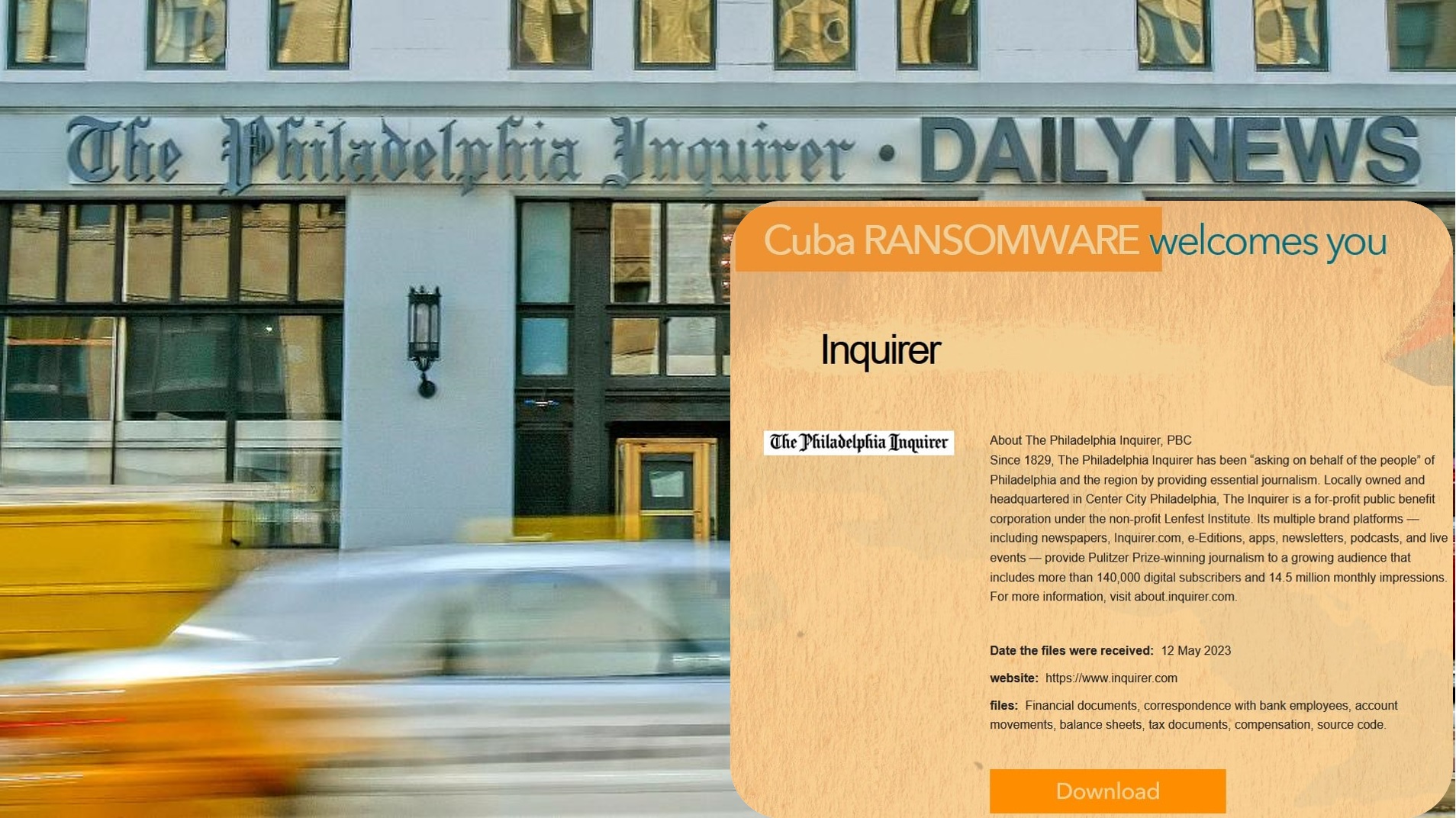
State-backed hackers from North Korea are conducting ransomware attacks against healthcare and critical infrastructure facilities to fund illicit activities, U.S. and South Korean cybersecurity and intelligence agencies warned in a joint advisory.
The attacks, which demand cryptocurrency ransoms in exchange for recovering access to encrypted files, are designed to support North Korea’s national-level priorities and objectives.
This includes “cyber operations targeting the United States and South Korea governments — specific targets include Department of Defense Information Networks and Defense Industrial Base member networks,” the authorities said
Rob Joyce NSA CS Director Tweeted “DPRK is actively ransoming Health Care and other critical infrastructure victims. Don’t give DPRK actors easy entry into your networks”.
Technical Details
This CSA is supplementary to previous reports on malicious cyber actor activities involving DPRK ransomware campaigns—namely Maui and H0lyGh0st ransomware. The authoring agencies are issuing this advisory to highlight additional observed TTPs DPRK cyber actors are using to conduct ransomware attacks targeting South Korean and U.S. healthcare systems.
Observable TTPs
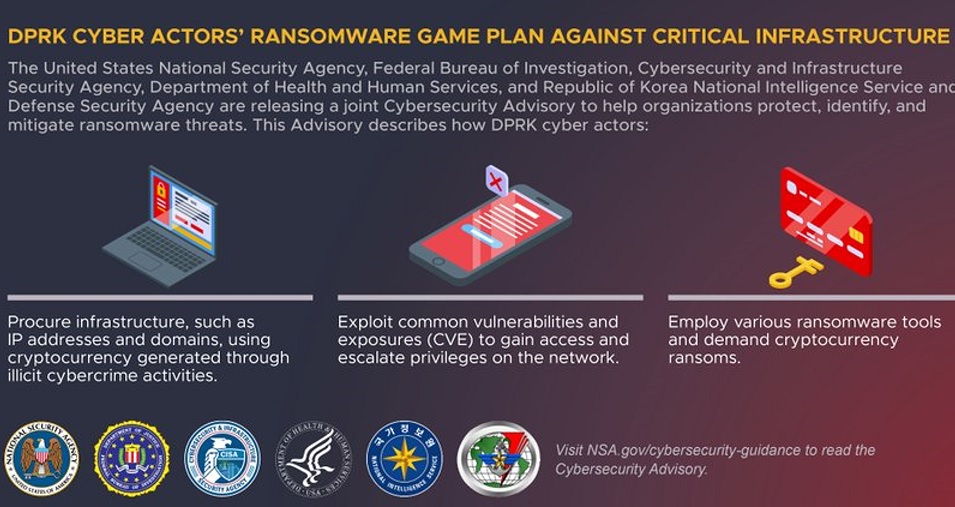
The TTPs associated with DPRK ransomware attacks include those traditionally observed in ransomware operations. Additionally, these TTPs span phases from acquiring and purchasing infrastructure to concealing DPRK affiliation:
Acquire Infrastructure [T1583]. DPRK actors generate domains, personas, and accounts; and identify cryptocurrency services to conduct their ransomware operations. Actors procure infrastructure, IP addresses, and domains with cryptocurrency generated through illicit cybercrime, such as ransomware and cryptocurrency theft.
Obfuscate Identity. DPRK actors purposely obfuscate their involvement by operating with or under third-party foreign affiliate identities and use third-party foreign intermediaries to receive ransom payments.
Purchase VPNs and VPSs [T1583.003]. DPRK cyber actors will also use virtual private networks (VPNs) and virtual private servers (VPSs) or third-country IP addresses to appear to be from innocuous locations instead of from DPRK.
Gain Access [TA0001]. Actors use various exploits of common vulnerabilities and exposures (CVE) to gain access and escalate privileges on networks. Recently observed CVEs that actors used to gain access include remote code execution in the Apache Log4j software library (known as Log4Shell) and remote code execution in unpatched SonicWall SMA 100 appliances [T1190 and T1133]. Observed CVEs used include:
CVE 2021-44228
CVE-2021-20038
CVE-2022-24990
Actors also likely spread malicious code through Trojanized files for “X-Popup,” an open source messenger commonly used by employees of small and medium hospitals in South Korea [T1195].
The actors spread malware by leveraging two domains: xpopup.pe[.]kr and xpopup.com. xpopup.pe[.]kr is registered to IP address 115.68.95[.]128 and xpopup[.]com is registered to IP address 119.205.197[.]111.
For additional information on state-sponsored DPRK malicious cyber activity, see CISA’s North Korea Cyber Threat Overview and Advisories